New research: 4 need-to-know consumer trends shaping 2024
Download ReportEXPERIENCE MANAGEMENT_
168极速赛车 Three suites to create exceptional customer
frontlines, high-performing teams, and
products people love.
All on one platform.
xm for
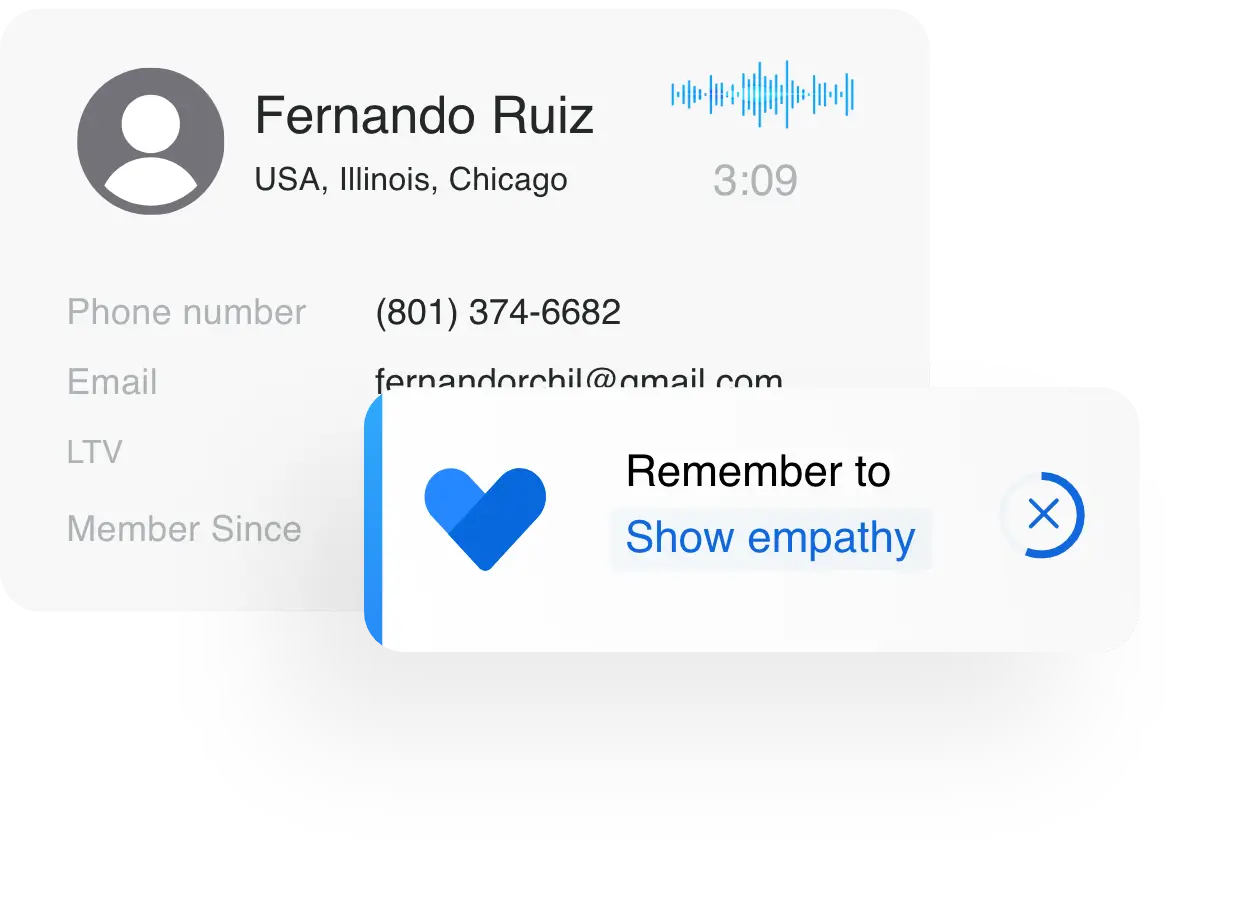
Customer Frontlines
Software to deliver better experiences
in contact centers and across every
digital and physical touchpoint.
 Digital
Digital
 Care
Care
 Locations
Locations
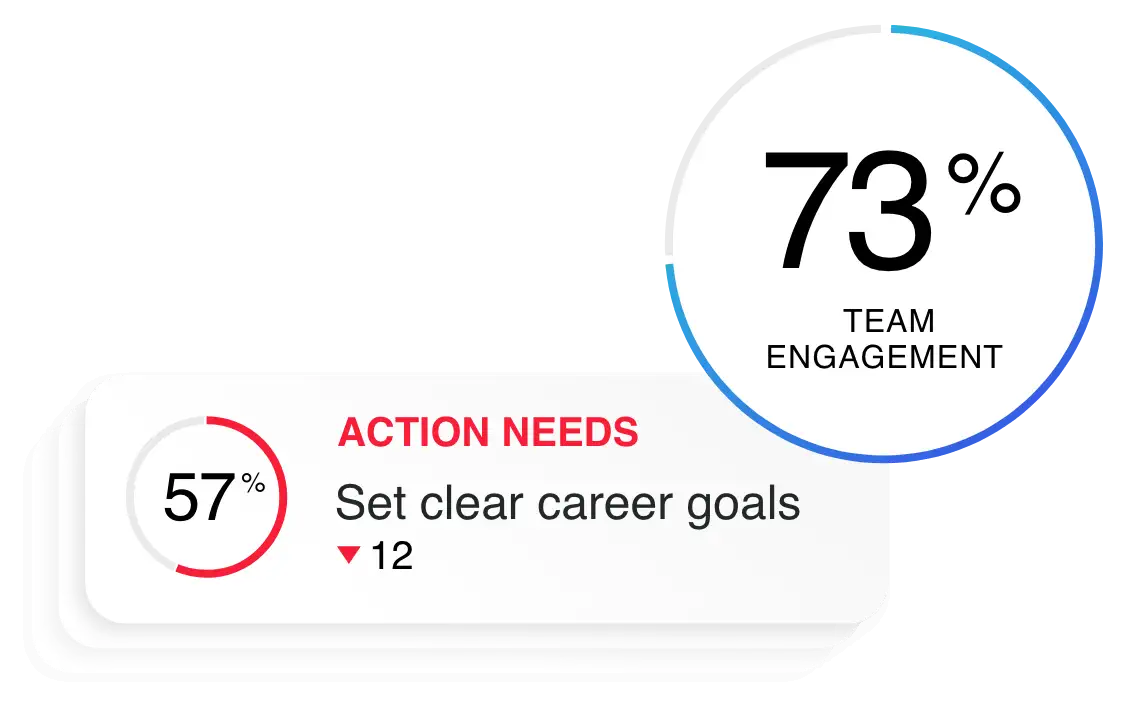
xm for
People Teams
Software to engage teams, improve
manager effectiveness, and make informed
people and business decisions.
 Engage
Engage
 Lifecycle
Lifecycle
 Analytics
Analytics
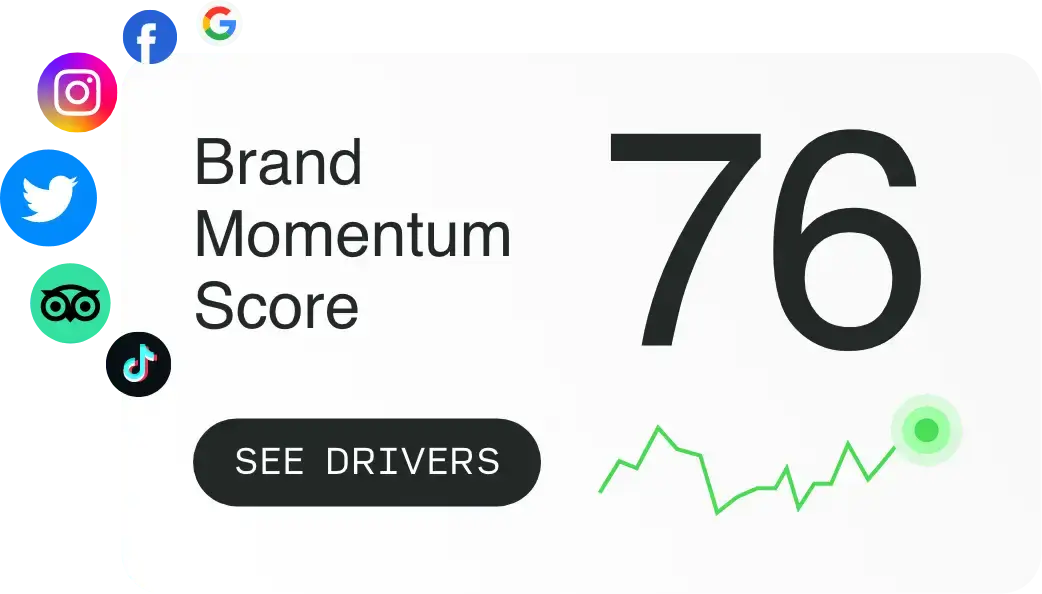
xm for
Strategy & Research
Software to design products
people love, increase market
share, and accelerate growth.
 Research
Research
 UX
UX
 Brand
Brand
XM Resources_
极速赛车官网开奖数据 168官方极速赛车开奖在线直播现场,168官网飞艇开奖记录 Explore Experience
Management
极速赛车一分钟 The World’s #1 XM Platform.
users
analyzed
analyst reports
platform
100 use Qualtrics
Stories of how the best brands and businesses win on experience.
Stream original series, documentary films, and more.
1分钟极速赛车官方开奖记录查询-极速赛车168开奖官网数据 Get started with
your
personalized demo
168极速赛车开奖官网开奖记录 一分钟极速赛车官方开奖直播 Complete the form to see the XM platform in action. We’ll show you how you can use Qualtrics to design and improve the experiences you deliver across your organization.